Unmasking Infostealer: Don't Believe What You See...
Introduction
Imagine stumbling across a seemingly harmless script while hunting for tools online, only to uncover a sophisticated malware designed to steal passwords, session tokens, and cookies. That’s exactly what happened to me, and it sent me down a rabbit hole of investigation. In this blog post, I’ll take you on that journey.
The Start of the Journey
It all began when I was searching GitHub for a HTTP flooding DoS script for penetration testing. Like everyone else, I was looking for existing code because, well, why reinvent the wheel, right? That’s when I stumbled upon a GitHub repository (Azepofff/Adv-DDOS) on the first page of my search results.

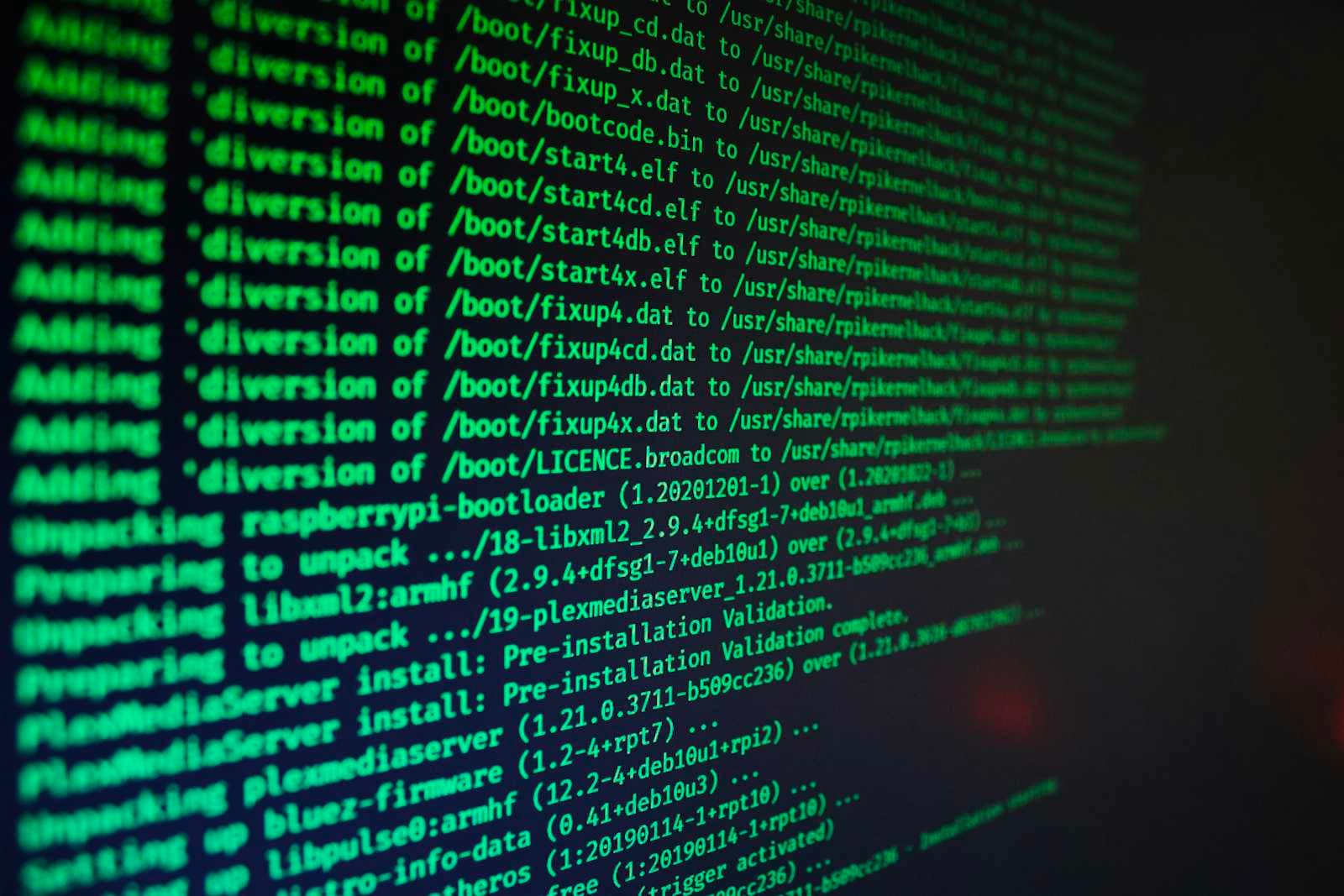
At first glance, the source code looked normal. But do you notice anything suspicious? Probably not, unless you scroll all the way to the right or click the "Raw" button on GitHub—which is how I noticed the malicious code.

Hidden at the end of the script, after a semicolon, was a line of code that installs the fernet module, decrypts an encrypted string, and executes it. This immediately raised a red flag, and I knew I had to dig deeper.
Digging Deeper
I decrypted the encrypted string locally (without executing it) and discovered a URL pointing to a suspicious domain: 1312services[.]ru. Naturally, my next step was to investigate this domain.

I tried accessing it via a browser, but Cloudflare blocked my request.

I attempted to use curl, but the request was still blocked.

Surprisingly, I managed to access the content using the Python requests module.

This revealed that Cloudflare was likely configured to block all requests except those with the default User-Agent header of the requests module. For reference, here’s the default User-Agent of the requests module (version 2.32.3): python-requests/2.32.3
For an added tip, you can send HTTP GET request to http://httpbin.org/headers to see the headers of your request without intercepting it.
Uncovering the Payload
The response contained Python code that created a file named gruppe.py under the C:\Users\<Username>\AppData\Roaming directory, clearly targeting Windows users. The script wrote a string stored in a content variable to this file and then executed it.

To further analyze this, I copied the string into another file. This revealed another Python script, which also decrypted an encrypted string and executed it. Upon decrypting this text, I uncovered 620 lines of Python code, which is the main payload script.

I’ve shared the payload code in this gist: https://gist.github.com/kcnaiamh/ad72bf34957eaf3c144f8a0899233128
Analyzing the Payload
Given the script’s size, I used ChatGPT to get a quick understanding of its functionality. Here’s what I found:
What the Script Does
This malware is designed to steal sensitive data from the victim’s system. It:
Targets Chromium-Based Browsers:
Steals passwords, cookies, and tokens by decrypting browser-stored credentials.
Extracts data from popular browsers like Chrome, Edge, Brave, and Opera.
Targets Cryptocurrency Wallets:
Accesses wallets such as MetaMask, Exodus, and Atomic Wallet.
Extracts data from browser extensions linked to these wallets.
Targets Messaging Apps:
- Extracts authentication tokens and session cookies from Discord and Telegram.
Searches for Sensitive Files:
- Scans common directories (e.g., Desktop, Documents) for files containing keywords like "password," "wallet," or "crypto."
Persistence Mechanism:
- Saves itself in the Windows Startup folder to ensure it runs on system reboot.
Overall Observation
Remember the domain name? I did a WHOIS lookup to gather more information.

While I didn’t dive too deeply, I suspect the GitHub user “Azepofff” may be linked to Russia. Every repository from this account is designed for deploying the infostealer malware. Groups like these typically steal credentials to further spread malware, infect systems with ransomware if they gain access to critical infrastructure, or sell initial access on hacker forums. They also pilfer cryptocurrency whenever possible.
This is their business model—and unfortunately, it seems to be a profitable one.
If you have the time, please consider reporting this GitHub user.
Final Thoughts
When using code from unknown sources, simply reading it isn’t enough. You need to dig deeper and examine hidden sections to ensure attackers haven’t sneakily inserted malicious code.